Douglas Stebila
Prototyping post-quantum and hybrid key exchange and authentication in TLS and SSH
Abstract
Once algorithms for quantum-resistant key exchange and digital signature schemes are selected by standards bodies, adoption of post-quantum cryptography will depend on progress in integrating those algorithms into standards for communication protocols and other parts of the IT infrastructure. In this paper, we explore how two major Internet security protocols, the Transport Layer Security (TLS) and Secure Shell (SSH) protocols, can be adapted to use post-quantum cryptography.
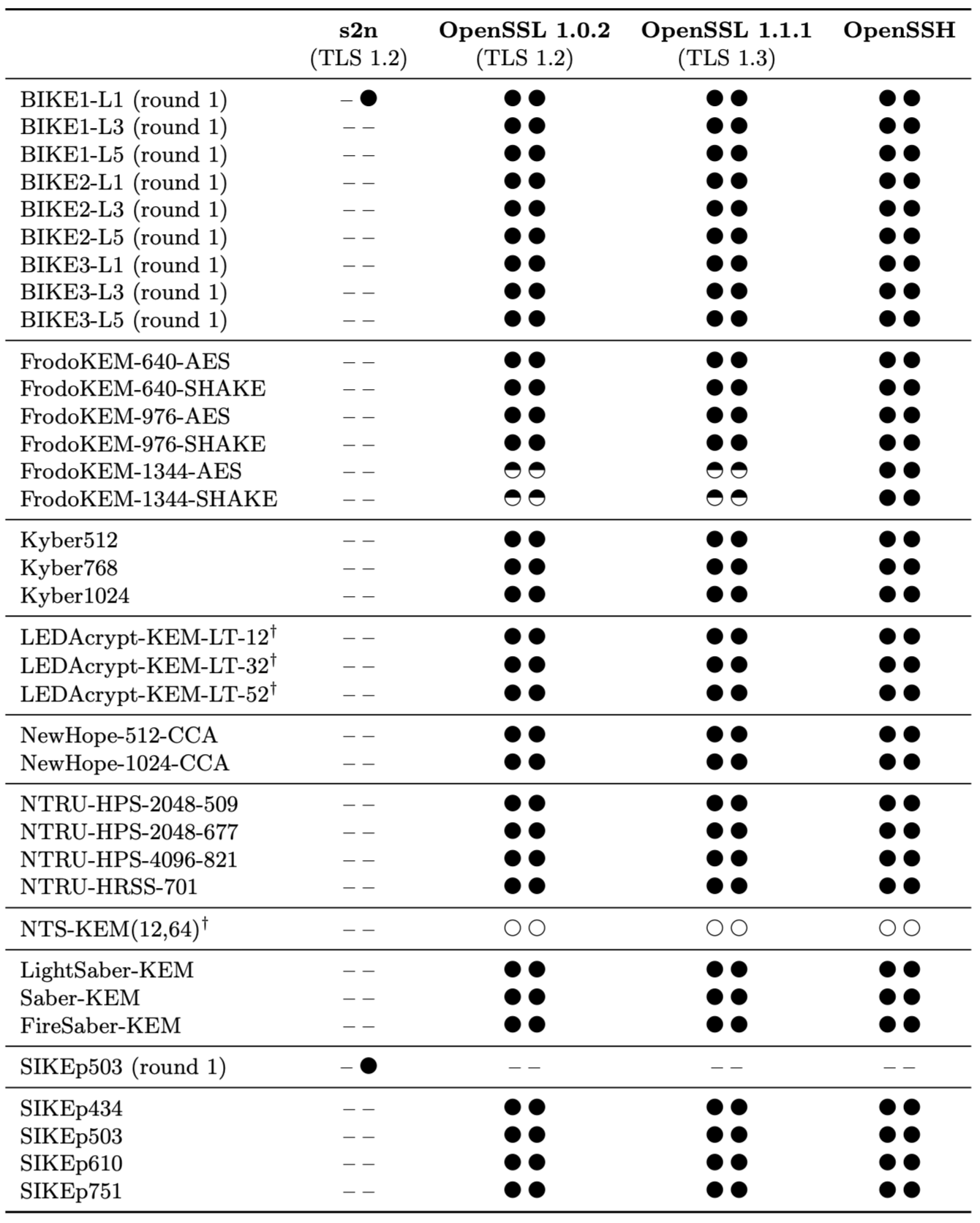
First, we examine various design considerations for integrating post-quantum and hybrid key exchange and authentication into communications protocols generally, and in TLS and SSH specifically. These include issues such as how to negotiate the use of multiple algorithms for hybrid cryptography, how to combine multiple keys, and more. Subsequently, we report on several implementations of post-quantum and hybrid key exchange in TLS 1.2, TLS 1.3, and SSHv2. We also report on work to add hybrid authentication in TLS 1.3 and SSHv2. These integrations are in Amazon s2n and forks of OpenSSL and OpenSSH; the latter two rely on the liboqs library from the Open Quantum Safe project.
Keywords: post-quantum cryptography, TLS, SSH
Reference
Eric Crockett, Christian Paquin, Douglas Stebila. Prototyping post-quantum and hybrid key exchange and authentication in TLS and SSH. In NIST 2nd Post-Quantum Cryptography Standardization Conference 2019. August 2019. © The authors.
Download
Presentations
- 2020-11-17: Indian Workshop on Post-Quantum Cryptography. (PDF slides)
- 2019-08-22: NIST 2nd Post-Quantum Cryptography Standardization Conference 2019, Santa Barbara, California. (PDF slides)
BibTeX
Funding
This research was supported by:- Natural Sciences and Engineering Research Council of Canada (NSERC) Discovery grant RGPIN-2016-05146
- NSERC Discovery Accelerator Supplement grant RGPIN-2016-05146