Douglas Stebila
Post-quantum TLS without handshake signatures
Abstract
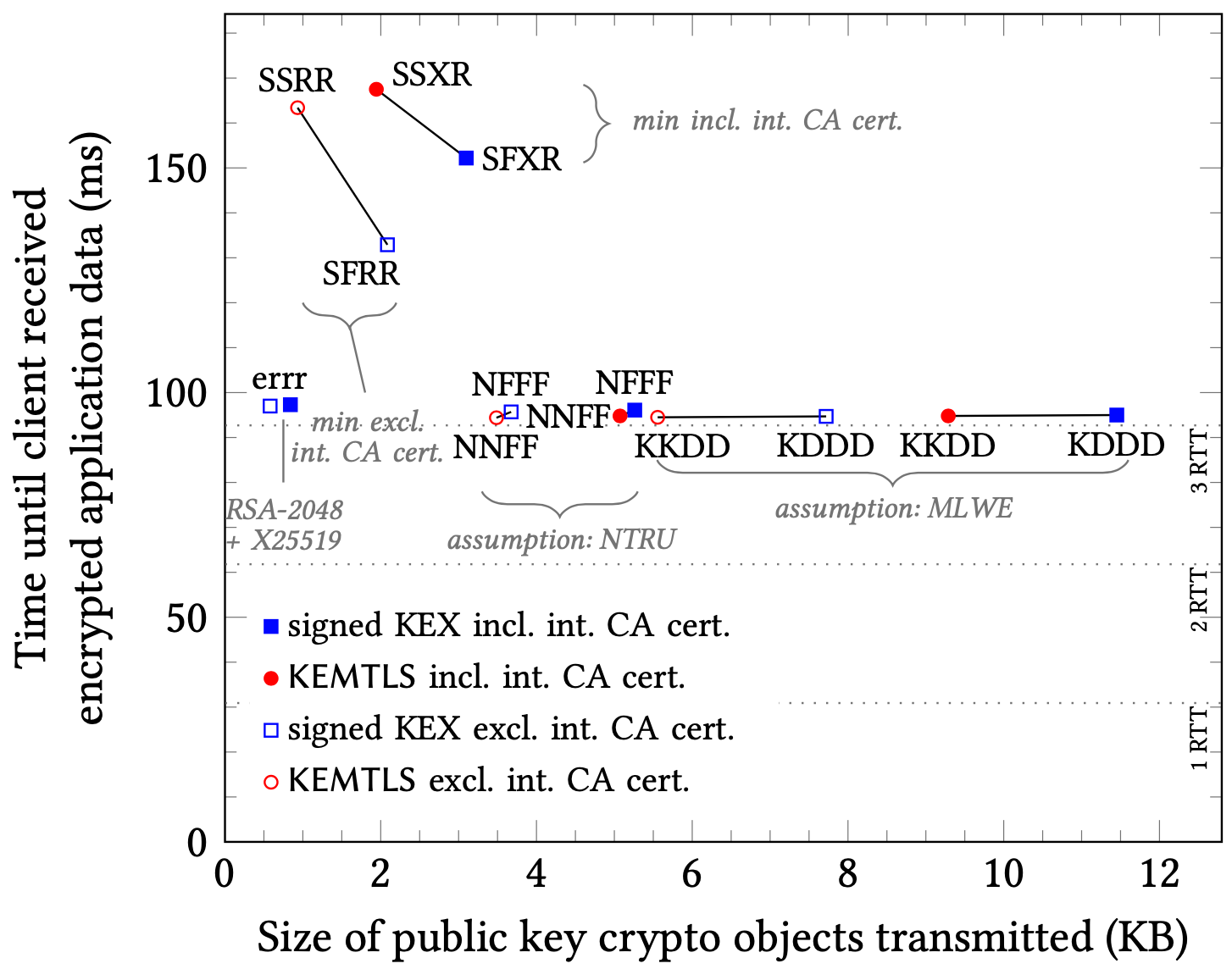
We present KEMTLS, an alternative to the TLS 1.3 handshake that uses key-encapsulation mechanisms (KEMs) instead of signatures for server authentication. Among existing post-quantum candidates, signature schemes generally have larger public key/signature sizes compared to the public key/ciphertext sizes of KEMs: by using an IND-CCA-secure KEM for server authentication in post-quantum TLS, we obtain multiple benefits. A size-optimized post-quantum instantiation of KEMTLS requires less than half the bandwidth of a size-optimized post-quantum instantiation of TLS 1.3. In a speed-optimized instantiation, KEMTLS reduces the amount of server CPU cycles by almost 90% compared to TLS 1.3, while at the same time reducing communication size, reducing the time until the client can start sending encrypted application data, and eliminating code for signatures from the server's trusted code base.
Keywords: post-quantum cryptography, key-encapsulation mechanisms, Transport Layer Security, NIST PQC
Reference
Peter Schwabe, Douglas Stebila, Thom Wiggers. Post-quantum TLS without handshake signatures. In Jonathan Katz, Giovanni Vigna, editors, Proc. 27th ACM Conference on Computer and Communications Security (CCS) 2020. ACM, November 2020. © The authors.
Download
Code
- Implementation and experimental data (GitHub)
Presentations
- 2022-05-12: Technology Innovation Institute. (PDF slides)
- 2021-05-13: Alphabet. (PDF slides)
- 2021-03-18: VMware PQC Forum. (PDF slides)
- 2021-02-05: CISPA Helmholtz Center for Information Security. (PDF slides)
- 2020-11-17: Indian Workshop on Post-Quantum Cryptography. (PDF slides)
Media
- 2021-01-25: The Daily Swig: KEMTLS: Cloudflare trials new encryption mechanism in anticipation of post-quantum TLS shortcomings.
- 2021-01-15: The Cloudflare Blog: KEMTLS: Post-quantum TLS without signatures.
BibTeX
Funding
This research was supported by:- Natural Sciences and Engineering Research Council of Canada (NSERC) Discovery grant RGPIN-2016-05146
- NSERC Discovery Accelerator Supplement grant RGPIN-2016-05146
- European Research Council Starting Grant No. 805031 (EPOQUE)