Douglas Stebila
Publicly verifiable ciphertexts (full version)
Abstract
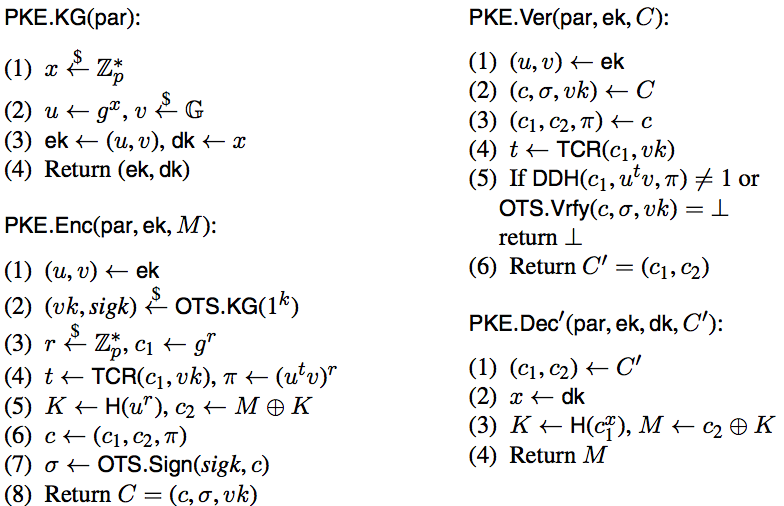
In many applications, where encrypted traffic flows from an open (public) domain to a protected (private) domain, there exists a gateway that bridges the two domains and faithfully forwards the incoming traffic to the receiver. We observe that indistinguishability against (adaptive) chosen-ciphertext attacks (IND-CCA), which is a mandatory goal in face of active attacks in a public domain, can be essentially relaxed to indistinguishability against chosen-plaintext attacks (IND-CPA) for ciphertexts once they pass the gateway that acts as an IND-CCA/CPA filter by first checking the validity of an incoming IND-CCA ciphertext, then transforming it (if valid) into an IND-CPA ciphertext, and forwarding the latter to the recipient in the private domain. “Non-trivial filtering” can result in reduced decryption costs on the receivers' side.
We identify a class of encryption schemes with publicly verifiable ciphertexts that admit generic constructions of (non-trivial) IND-CCA/CPA filters. These schemes are characterized by existence of public algorithms that can distinguish between valid and invalid ciphertexts. To this end, we formally define (non-trivial) public verifiability of ciphertexts for general encryption schemes, key encapsulation mechanisms, and hybrid encryption schemes, encompassing public-key, identity-based, and tag-based encryption flavours. We further analyze the security impact of public verifiability and discuss generic transformations and concrete constructions that enjoy this property.
Keywords: ciphertext filtering, public key encryption, identity-based encryption, chosen ciphertext attacks
Reference
Juan González Nieto, Mark Manulis, Bertram Poettering, Jothi Rangasamy, Douglas Stebila. Publicly verifiable ciphertexts (full version). Journal of Computer Security, 21(5):749-778. September 2013. Extended abstract published in SCN 2012. © IOS Press.
Download
BibTeX
Funding
This research was supported by:- the Australian Technology Network and German Academic Exchange Service (ATN-DAAD) Joint Research Co-operation Scheme
- Australia–India Strategic Research Fund (AISRF) project TA020002
- German Research Foundation (DFG) grant MA 4957
- Hessian LOEWE excellence initiative within the Center of Advanced Security Research Darmstadt (CASED)
- European Center for Security and Privacy by Design (EC SPRIDE)