Douglas Stebila
Protecting encrypted cookies from compression side-channel attacks
Abstract
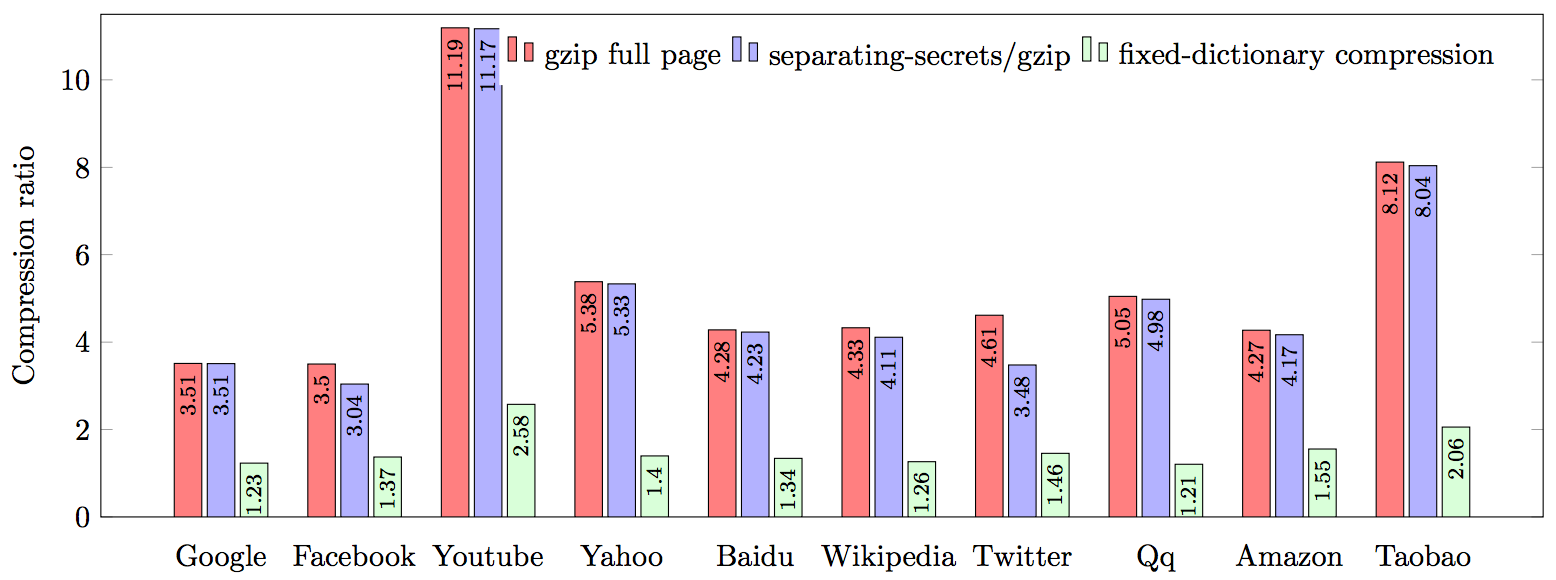
Compression is desirable for network applications as it saves bandwidth; however, when data is compressed before being encrypted, the amount of compression leaks information about the amount of redundancy in the plaintext. This side channel has led to successful CRIME and BREACH attacks on web traffic protected by the Transport Layer Security (TLS) protocol. The general guidance in light of these attacks has been to disable compression, preserving confidentiality but sacrificing bandwidth. In this paper, we examine two techniques---heuristic separation of secrets and fixed-dictionary compression---for enabling compression while protecting high-value secrets, such as cookies, from attack. We model the security offered by these techniques and report on the amount of compressibility that they can achieve.
Reference
Janaka Alawatugoda, Douglas Stebila, Colin Boyd. Protecting encrypted cookies from compression side-channel attacks. In Rainer Böhme, Tatsuaki Okamoto, editors, Proc. 19th International Conference on Financial Cryptography and Data Security (FC) 2015, LNCS, vol. 8975, pp. 86-106. Springer, January 2015. © IFCA.
Download
Presentations
- 2015-11-27: University of Otago, Dunedin, New Zealand. (PDF slides)
- 2015-02-18: Microsoft Research, Cambridge. (PDF slides)
- 2015-01-22: Royal Holloway, University of London. (PDF slides)
BibTeX
Funding
This research was supported by:- Australian Research Council (ARC) Discovery Project grant DP130104304