Douglas Stebila
A cryptographic analysis of the TLS 1.3 handshake protocol candidates
Abstract
The Internet Engineering Task Force (IETF) is currently developing the next version of the Transport Layer Security (TLS) protocol, version 1.3. The transparency of this standardization process allows comprehensive cryptographic analysis of the protocols prior to adoption, whereas previous TLS versions have been scrutinized in the cryptographic literature only after standardization. This is even more important as there are two related, yet slightly different, candidates in discussion for TLS 1.3, called draft-ietf-tls-tls13-05 and draft-ietf-tls-tls13-dh-based.
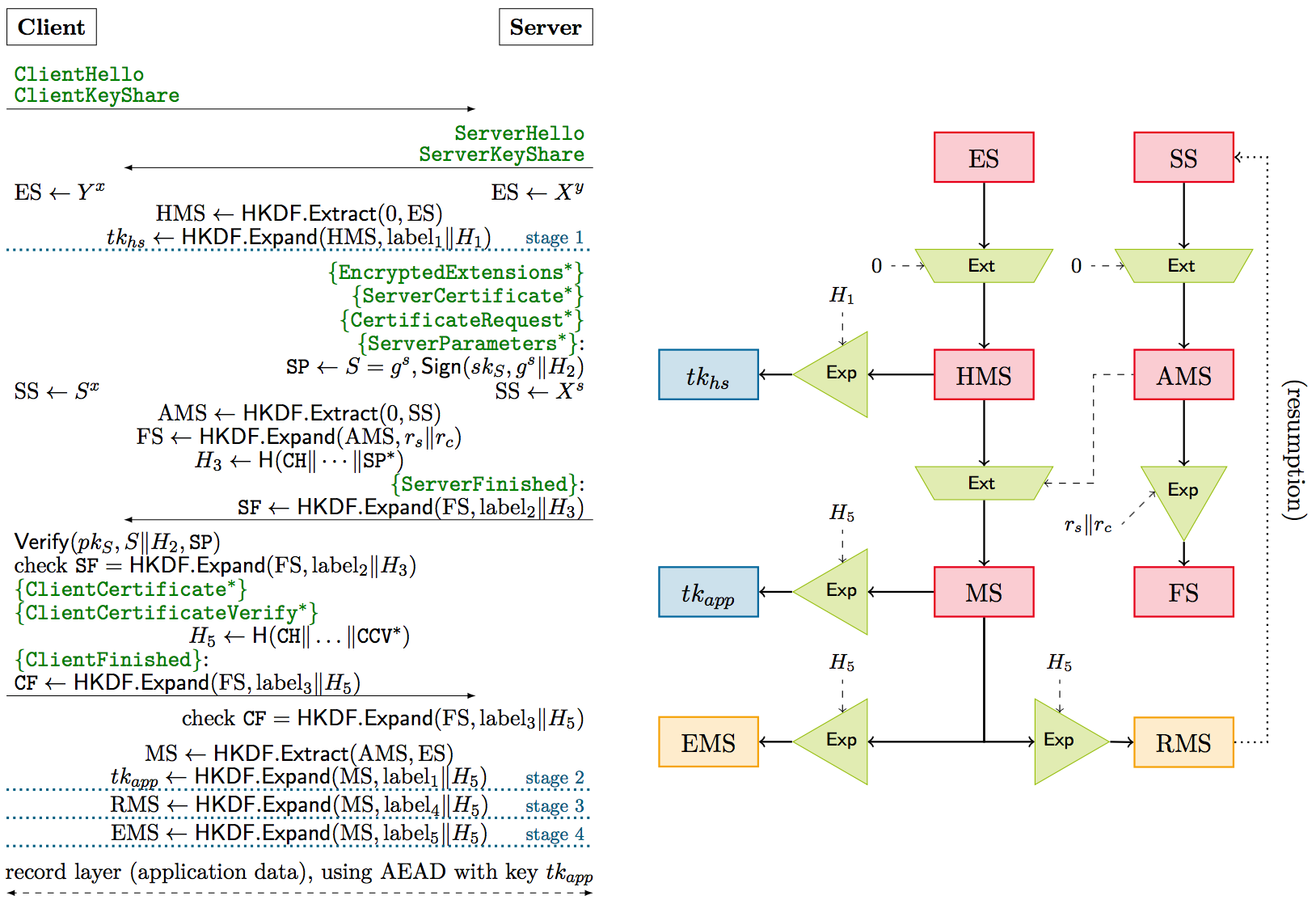
We give a cryptographic analysis of the primary ephemeral Diffie–Hellman-based handshake protocol, which authenticates parties and establishes encryption keys, of both TLS 1.3 candidates. We show that both candidate handshakes achieve the main goal of providing secure authenticated key exchange according to an augmented multi-stage version of the Bellare–Rogaway model. Such a multi-stage approach is convenient for analyzing the design of the candidates, as they establish multiple session keys during the exchange.
An important step in our analysis is to consider compositional security guarantees. We show that, since our multi-stage key exchange security notion is composable with arbitrary symmetric-key protocols, the use of session keys in the record layer protocol is safe. Moreover, since we can view the abbreviated TLS resumption procedure also as a symmetric-key protocol, our compositional analysis allows us to directly conclude security of the combined handshake with session resumption.
We include a discussion on several design characteristics of the TLS 1.3 drafts based on the observations in our analysis.
Keywords: Transport Layer Security (TLS), key exchange, protocol analysis, composition
Reference
Benjamin Dowling, Marc Fischlin, Felix Günther, Douglas Stebila. A cryptographic analysis of the TLS 1.3 handshake protocol candidates. In Proc. 22nd ACM Conference on Computer and Communications Security (CCS) 2015, pp. 1197-1210. ACM, October 2015. © ACM.
Download
BibTeX
Funding
This research was supported by:- Australian Research Council (ARC) Discovery Project grant DP130104304
- Heisenberg grant Fi 940/3-2 of the German Research Foundation (DFG) as part of project S4 within the CRC~1119 CROSSING