Douglas Stebila
Predicate-based key exchange
Abstract
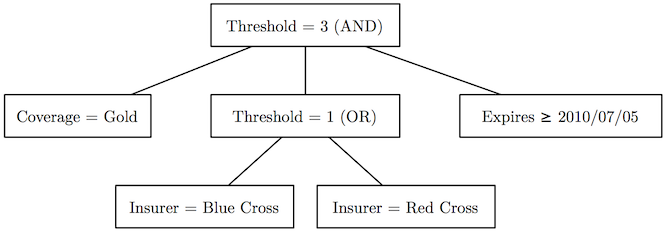
We provide the first description of and security model for authenticated key exchange protocols with predicate-based authentication. In addition to the standard goal of session key security, our security model also provides for credential privacy: a participating party learns nothing more about the other party's credentials than whether they satisfy the given predicate. Our model also encompasses attribute-based key exchange since it is a special case of predicate-based key exchange.
We demonstrate how to realize a secure predicate-based key exchange protocol by combining any secure predicate-based signature scheme with the basic Diffie-Hellman key exchange protocol, providing an efficient and simple solution.
Keywords: predicate-based, attribute-based, key exchange, protocols, security models, cryptography
Reference
James Birkett, Douglas Stebila. Predicate-based key exchange. In Ron Steinfeld, Philip Hawkes, editors, Proc. 15th Australasian Conference on Information Security and Privacy (ACISP) 2010, LNCS, vol. 6168, pp. 282-299. Springer, July 2010. © Springer.
Download
Presentations
- 2010-07-06: ACISP 2010. Presented by James Birkett (PDF slides)
BibTeX
Funding
This research was supported by:- Australian Research Council (ARC) Discovery Project grant DP0666065