Douglas Stebila
Modelling ciphersuite and version negotiation in the TLS protocol
Abstract
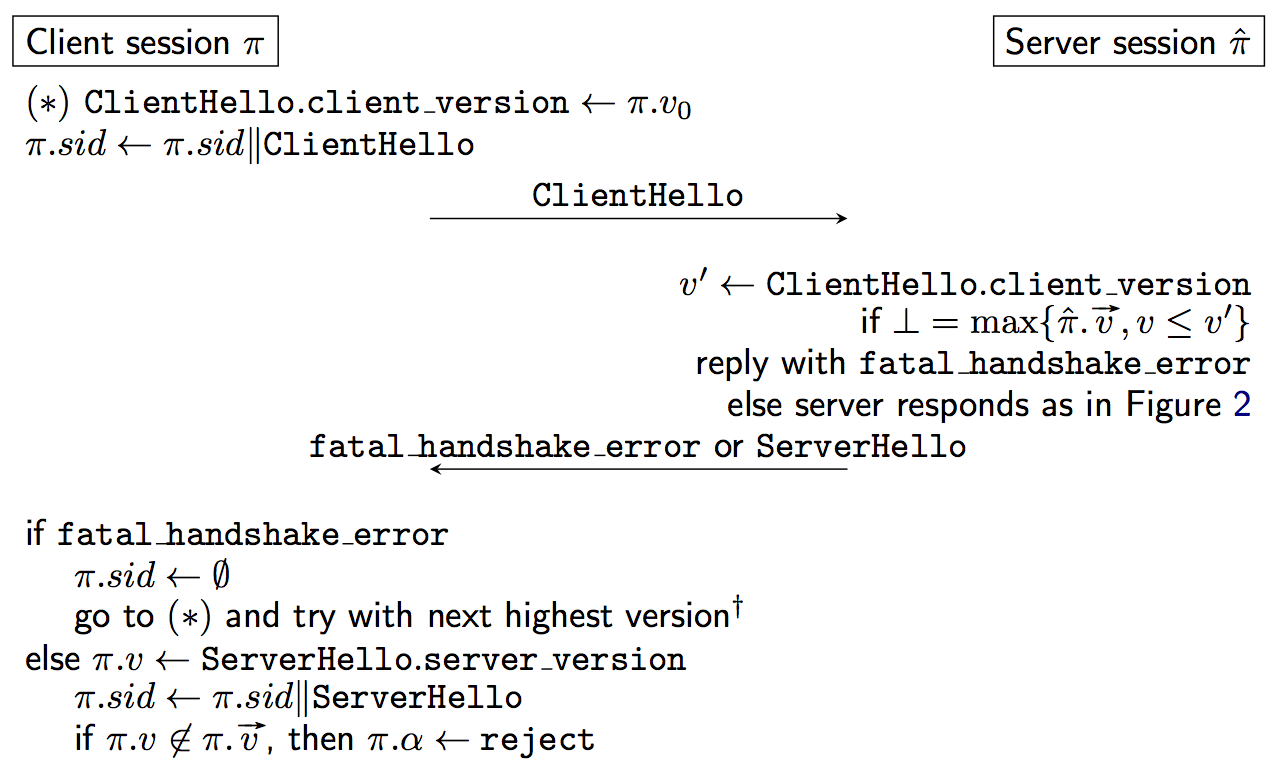
Real-world cryptographic protocols such as the widely used Transport Layer Security (TLS) protocol support many different combinations of cryptographic algorithms (called ciphersuites) and simultaneously support different versions. Recent advances in provable security have shown that most modern TLS ciphersuites are secure authenticated and confidential channel establishment (ACCE) protocols, but these analyses generally focus on single ciphersuites in isolation. In this paper we extend the ACCE model to cover protocols with many different sub-protocols, capturing both multiple ciphersuites and multiple versions, and define a security notion for secure negotiation of the optimal sub-protocol. We give a generic theorem that shows how secure negotiation follows, with some additional conditions, from the authentication property of secure ACCE protocols. Using this framework, we analyse the security of ciphersuite and three variants of version negotiation in TLS, including a recently proposed mechanism for detecting fallback attacks.
Keywords: Transport Layer Security (TLS), ciphersuite negotiation, version negotiation, downgrade attacks, cryptographic protocols
Reference
Benjamin Dowling, Douglas Stebila. Modelling ciphersuite and version negotiation in the TLS protocol. In Ernest Foo, Douglas Stebila, editors, Proc. 20th Australasian Conference on Information Security and Privacy (ACISP) 2015, LNCS, vol. 9144, pp. 270–288. Springer, June 2015. © Springer.
Download
BibTeX
Funding
This research was supported by:- Australian Research Council (ARC) Discovery Project grant DP130104304